Unveiling the Secrets of Exploitation: A Comprehensive Guide to Hacking The Art Of Exploitation 2nd Edition

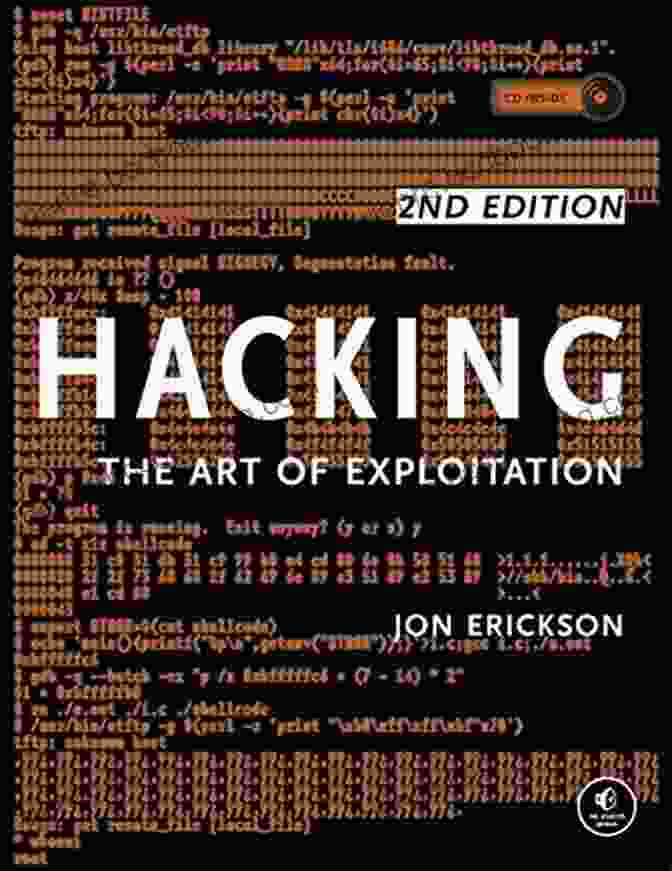
In the ever-evolving landscape of cybersecurity, understanding the art of exploitation is paramount for protecting your systems and preventing malicious attacks. "Hacking The Art Of Exploitation 2nd Edition" offers a comprehensive guide that delves into the intricate techniques employed by hackers, empowering you to safeguard your digital assets and stay ahead of emerging threats. This book is an invaluable resource for security researchers, penetration testers, ethical hackers, and anyone seeking to enhance their knowledge of exploitation techniques.
4.7 out of 5
| Language | : | English |
| File size | : | 1960 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Print length | : | 681 pages |
Exploring the Depths of Exploitation
The 2nd edition of "Hacking The Art Of Exploitation" meticulously dissects the art of exploitation, shedding light on advanced concepts and practical applications. It delves into various operating systems, including Windows, Linux, and macOS, providing a thorough understanding of each platform's security mechanisms and potential vulnerabilities. The book covers essential topics such as:
- In-depth analysis of memory corruption vulnerabilities, including buffer overflows, heap overflows, and format string vulnerabilities
- Advanced shellcoding techniques to gain complete control over the target system
- Exploitation of web applications, including XSS, SQL injection, and remote file inclusion
- Modern exploitation techniques, such as return-oriented programming (ROP) and just-in-time (JIT) compilation
- Countermeasures and detection techniques to protect systems from exploitation
Real-World Scenarios and Case Studies
Beyond theoretical explanations, "Hacking The Art Of Exploitation 2nd Edition" provides numerous real-world scenarios and case studies that illustrate the practical application of exploitation techniques. These case studies dissect real-world incidents, tracing the attacker's steps from initial reconnaissance to successful exploitation. By examining these examples, readers gain a deeper understanding of how exploitation is executed and can apply the lessons learned to enhance their security posture.
A Comprehensive Reference for Security Professionals
"Hacking The Art Of Exploitation 2nd Edition" is an indispensable reference for security professionals at all levels. It offers a comprehensive overview of exploitation techniques, arming readers with the knowledge and skills necessary to protect their systems from malicious attacks. The book also covers:
- Legal and ethical implications of exploitation techniques
- Best practices for secure coding and system hardening
- Tools and resources for vulnerability assessment and exploitation
A Must-Read for Aspiring Hackers
Aspiring hackers seeking to delve into the art of exploitation will find "Hacking The Art Of Exploitation 2nd Edition" an invaluable resource. The book provides a solid foundation in vulnerability research, exploitation techniques, and security best practices. With a clear and concise writing style, the authors empower readers to develop a deep understanding of the subject matter and hone their hacking skills.
Exceptional Value and Timeliness
The 2nd edition of "Hacking The Art Of Exploitation" is an exceptional value for security professionals and aspiring hackers alike. It is thoroughly updated to reflect the latest advancements in exploitation techniques and industry best practices. The book offers a wealth of information that is difficult to find elsewhere, making it a must-have resource for anyone serious about securing their systems and understanding the art of exploitation.
"Hacking The Art Of Exploitation 2nd Edition" is the definitive guide to exploitation techniques for security professionals and aspiring hackers. It provides a comprehensive overview of vulnerability research, practical exploitation techniques, and real-world case studies. The book is thoroughly updated to reflect the latest advancements in the field, making it an indispensable resource for anyone seeking to protect their systems and stay ahead of emerging threats. Invest in "Hacking The Art Of Exploitation 2nd Edition" today and empower yourself with the knowledge and skills to navigate the complex landscape of cybersecurity.
4.7 out of 5
| Language | : | English |
| File size | : | 1960 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Print length | : | 681 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Tom Wright
Tom Wright Samantha Giles
Samantha Giles Leland Melvin
Leland Melvin Linda Davick
Linda Davick Clive Webb
Clive Webb Nicholas R Jones
Nicholas R Jones Len Mcdougall
Len Mcdougall Thomas Achatz
Thomas Achatz Lee Jackson
Lee Jackson Lisa Pietsch
Lisa Pietsch Leonie Frieda
Leonie Frieda Lex Ronin
Lex Ronin T M Cromer
T M Cromer Val Waldeck
Val Waldeck Lavonne Mueller
Lavonne Mueller Mark Cheverton
Mark Cheverton Stefan C Reif
Stefan C Reif S Ali Myers
S Ali Myers Linda L French
Linda L French Merih Taze
Merih Taze
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Fyodor DostoevskyUnveiling the Legendary Hollywood Dynasty: An Exclusive Look into the Lives...
Fyodor DostoevskyUnveiling the Legendary Hollywood Dynasty: An Exclusive Look into the Lives...
 Simon MitchellTeen Organization Mastery: The Ultimate Guide to Unclutter Your Space and...
Simon MitchellTeen Organization Mastery: The Ultimate Guide to Unclutter Your Space and...
 Cade SimmonsLa Justice Des Mineurs: Un Voyage dans les Profondeurs du Système de Justice...
Cade SimmonsLa Justice Des Mineurs: Un Voyage dans les Profondeurs du Système de Justice...
 Michael CrichtonBecky Bunny And The Best Easter Ever: An Inspirational And Fun Easter Story...
Michael CrichtonBecky Bunny And The Best Easter Ever: An Inspirational And Fun Easter Story... Gavin MitchellFollow ·2.4k
Gavin MitchellFollow ·2.4k Geoffrey BlairFollow ·3.8k
Geoffrey BlairFollow ·3.8k DeShawn PowellFollow ·17.9k
DeShawn PowellFollow ·17.9k Anton ChekhovFollow ·7.9k
Anton ChekhovFollow ·7.9k Mario Vargas LlosaFollow ·14.5k
Mario Vargas LlosaFollow ·14.5k Jim CoxFollow ·5.4k
Jim CoxFollow ·5.4k Steve CarterFollow ·7.9k
Steve CarterFollow ·7.9k Jarrett BlairFollow ·19.5k
Jarrett BlairFollow ·19.5k

 Branden Simmons
Branden SimmonsUnveiling the World of Tequila: A Collector's Guide to...
: Prepare to embark on a tantalizing journey...
 Chuck Mitchell
Chuck MitchellHazel McCallion and the Development of Mississauga: A...
: The Matriarch of Mississauga Hazel...
 Lucas Reed
Lucas ReedUnveiling the Hidden Treasures of Tequila, Mezcal, and...
Prepare to be captivated...
 Isaias Blair
Isaias BlairBusinesses With Stories: The Power of Storytelling in...
In today's competitive business environment,...
 Ethan Gray
Ethan GrayUnveiling the World of Tequila, Mezcal, and Sotol: The...
Embark on a...
 Barry Bryant
Barry BryantClare Boothe Luce: Renaissance Woman
In the annals of history, few...
4.7 out of 5
| Language | : | English |
| File size | : | 1960 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Print length | : | 681 pages |